Shared Secrets¶
A secret is an object that contains a small amount of sensitive data such as a password, token, or key. Shared secrets can be added to container secrets.
Secrets are similar to ConfigMaps but are specifically intended to hold confidential data.
Accessing Shared Secrets¶
-
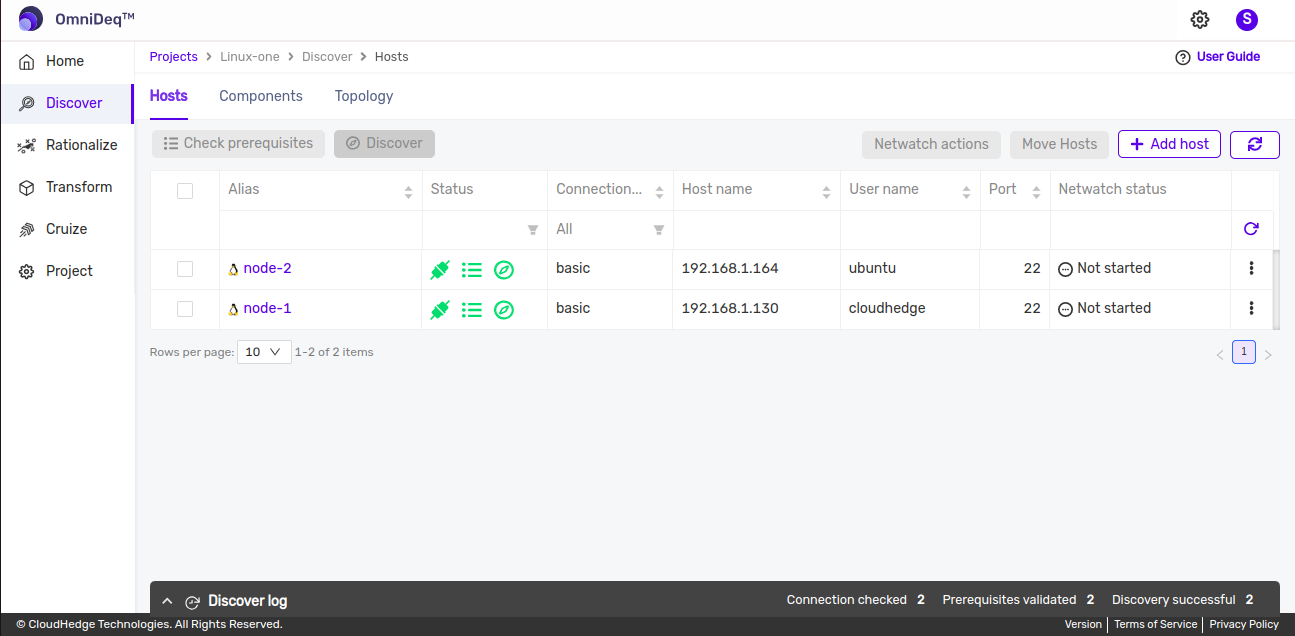
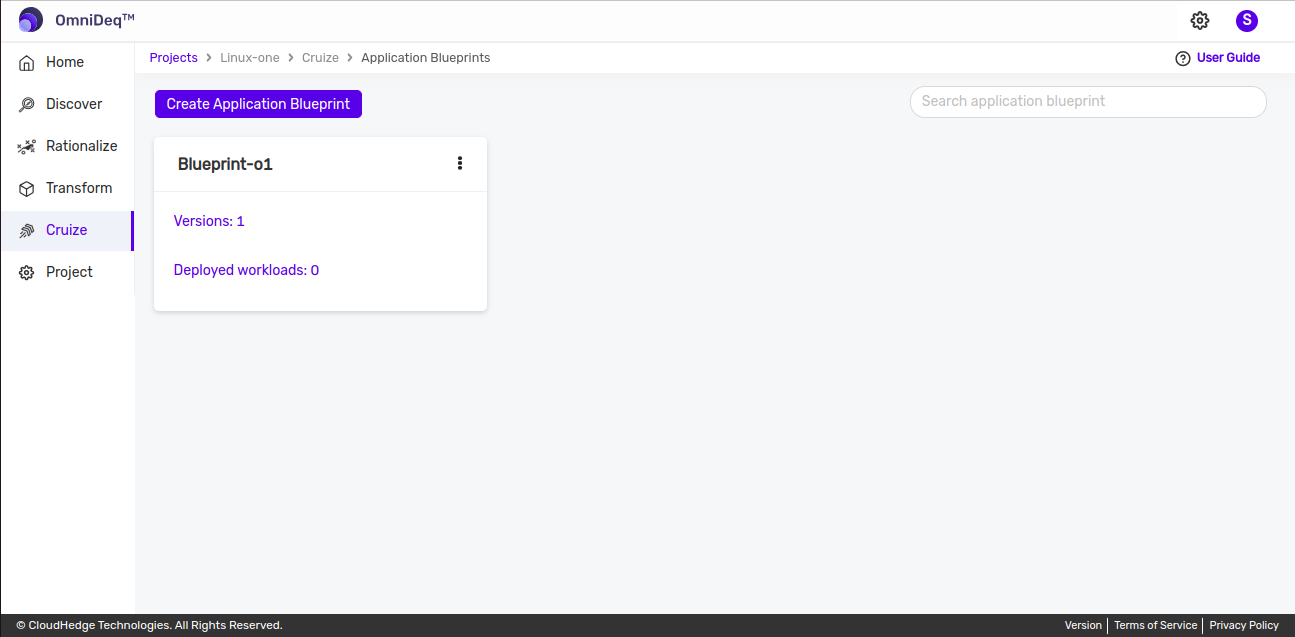
After logging into CHAI™, click on the project where you want to add shared secrets, then click Cruize.
-
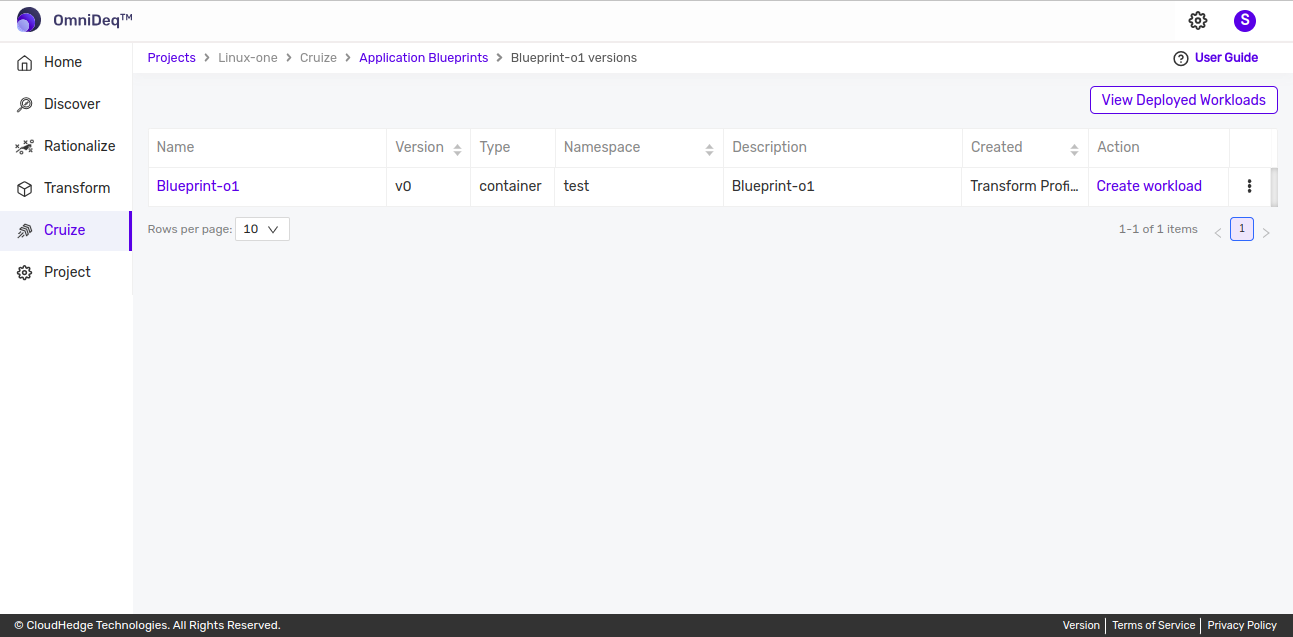
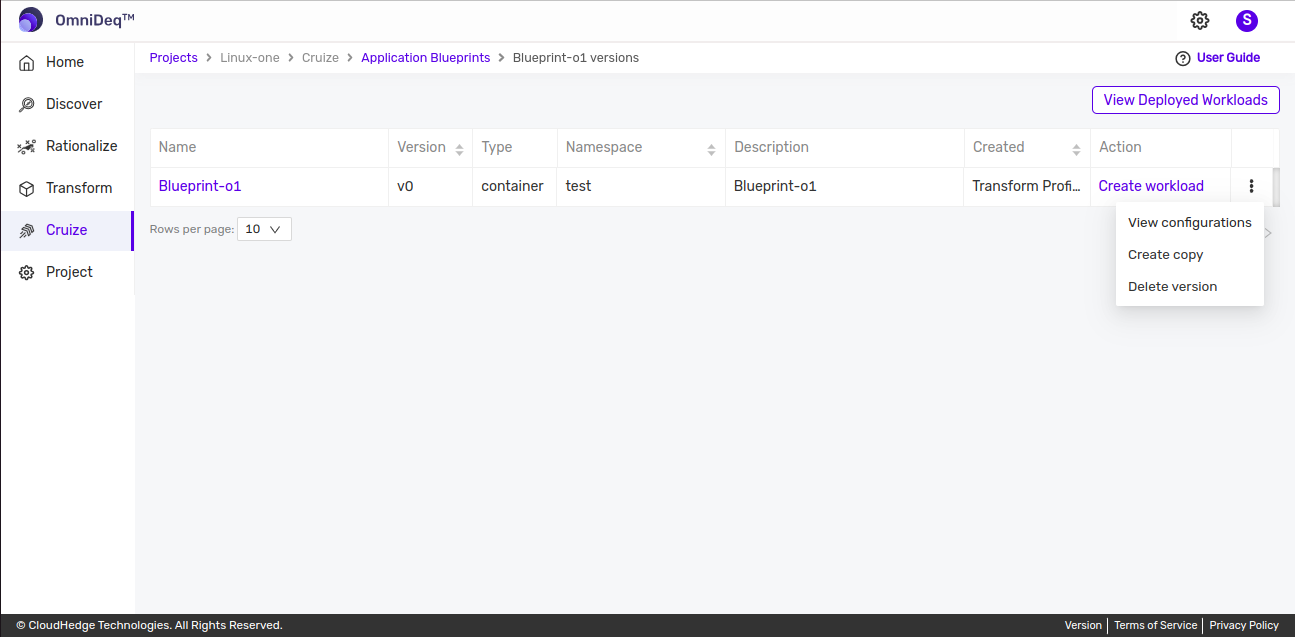
Click on the blueprint version count on the blueprint card. After clicking the count, the blueprint versions page will be displayed, which contains a list of blueprint versions as shown in the image below.
-
Click on the View configurations kebab menu option or click on the blueprint version name to view blueprint configurations.
-
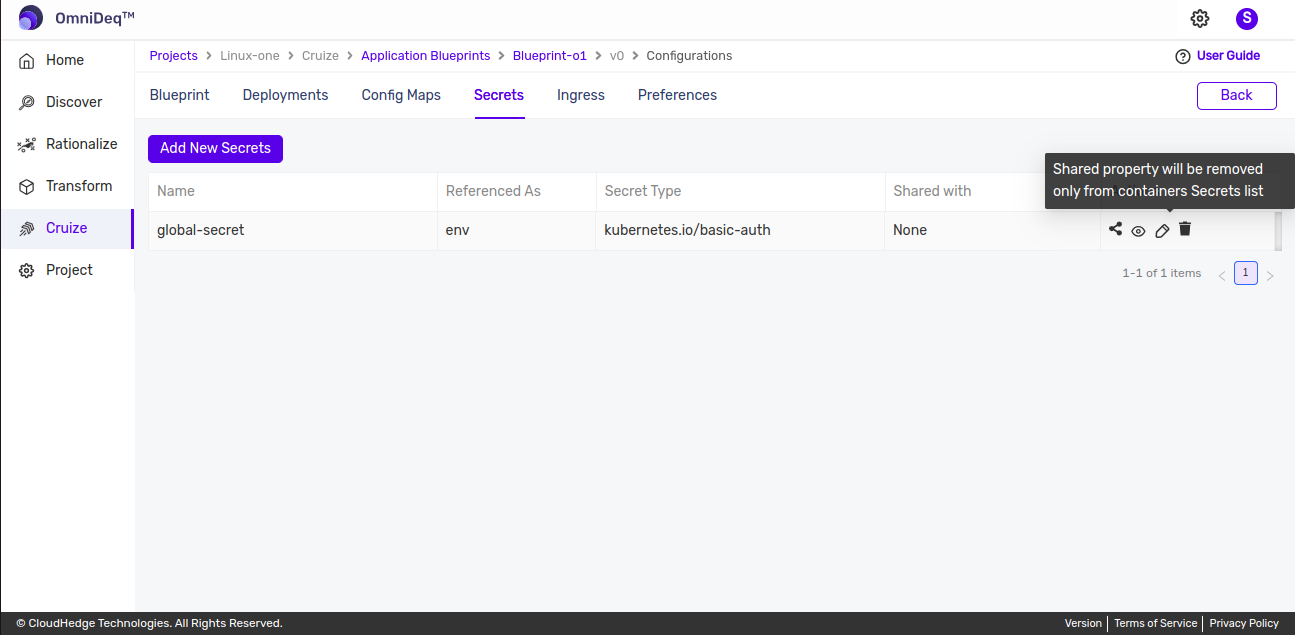
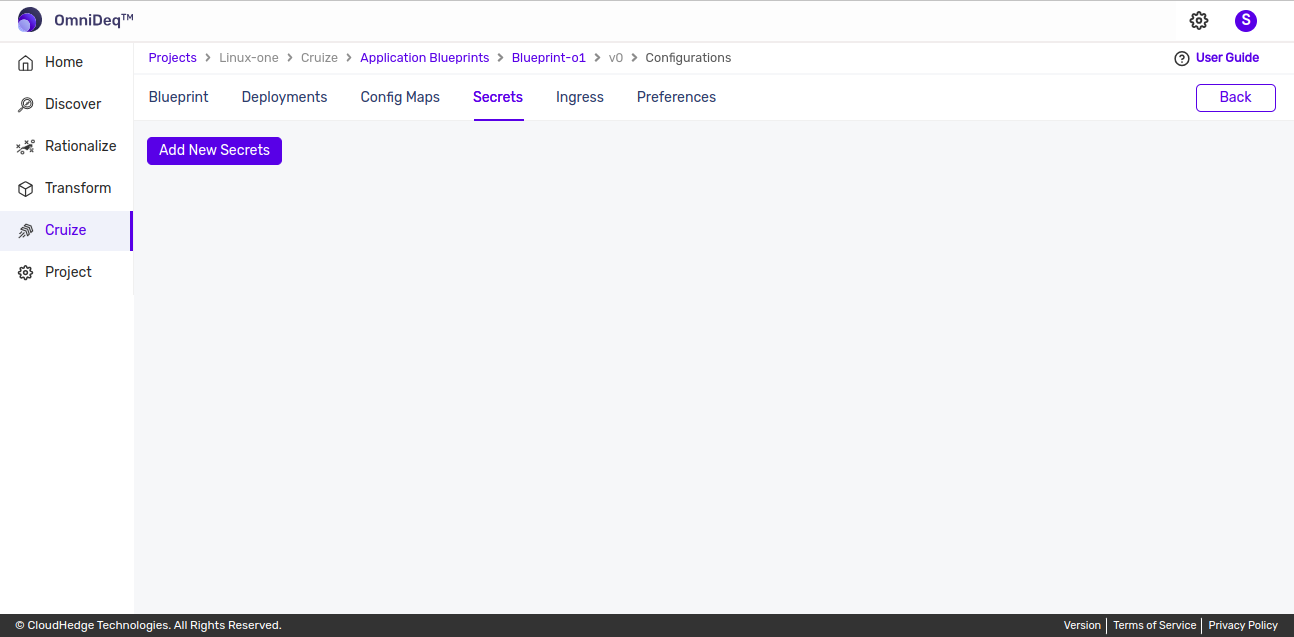
After clicking the above options, the blueprint configurations page will open. Then go to the Secrets tab beside the config maps tab as shown in the image below.
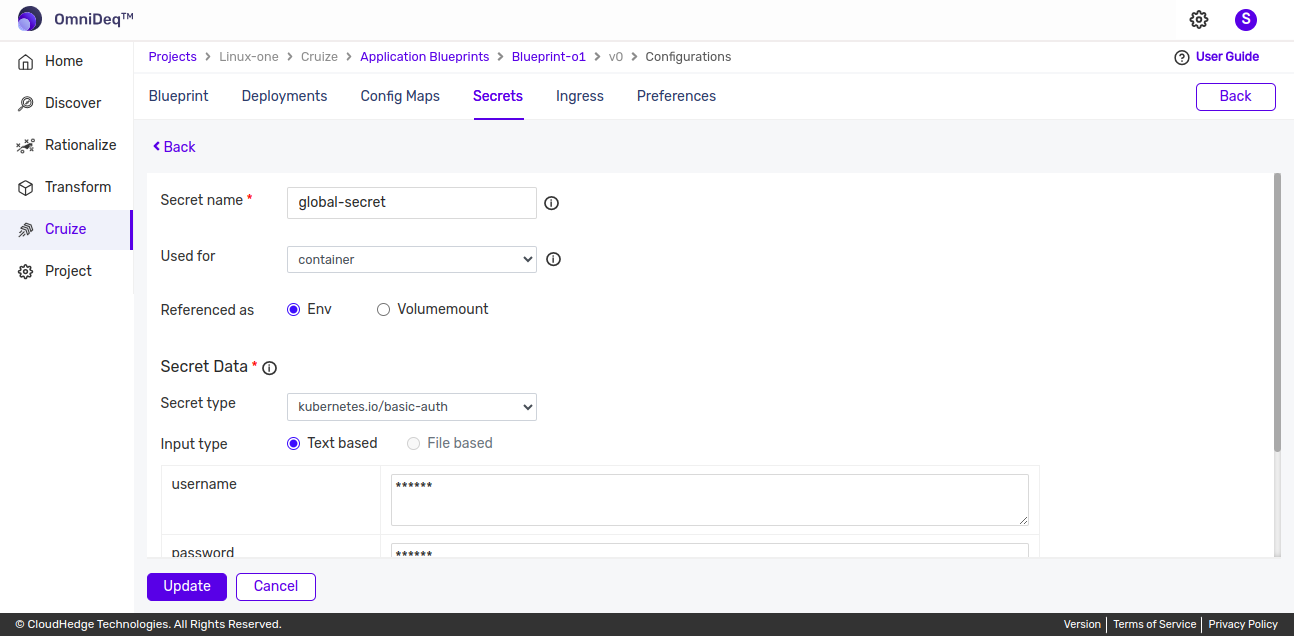
Adding a Secret¶
-
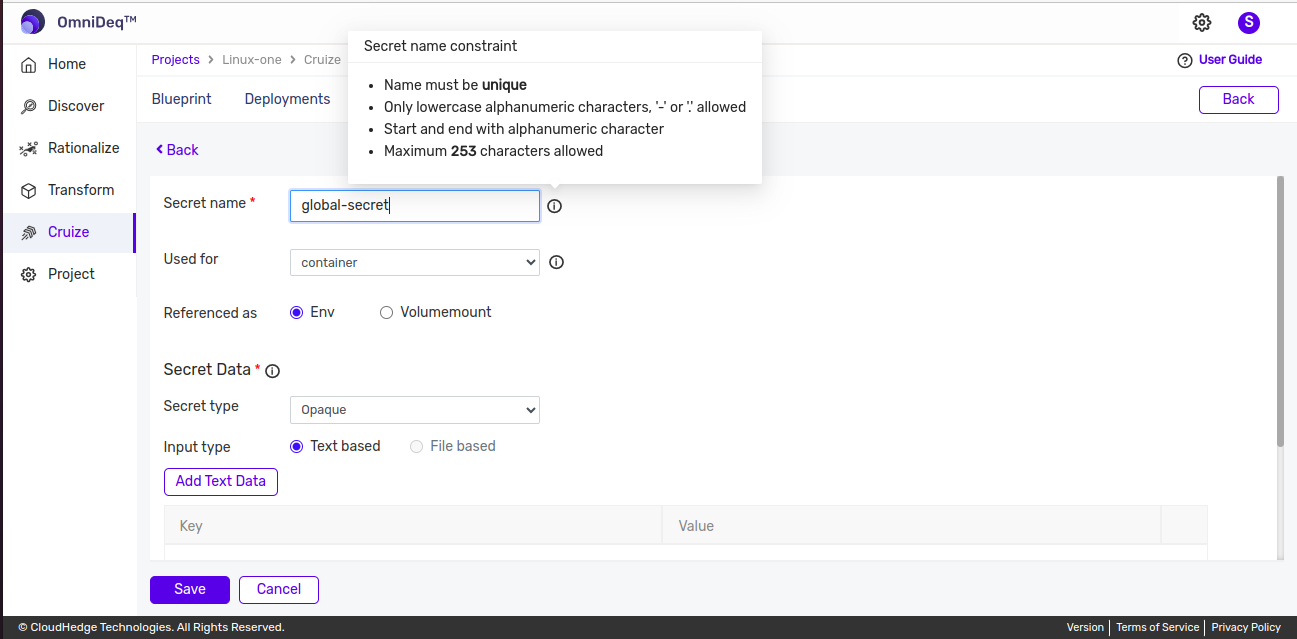
Click the Add New Secrets button from the Secrets tab. A form will be displayed to add a secret as shown in the image below.
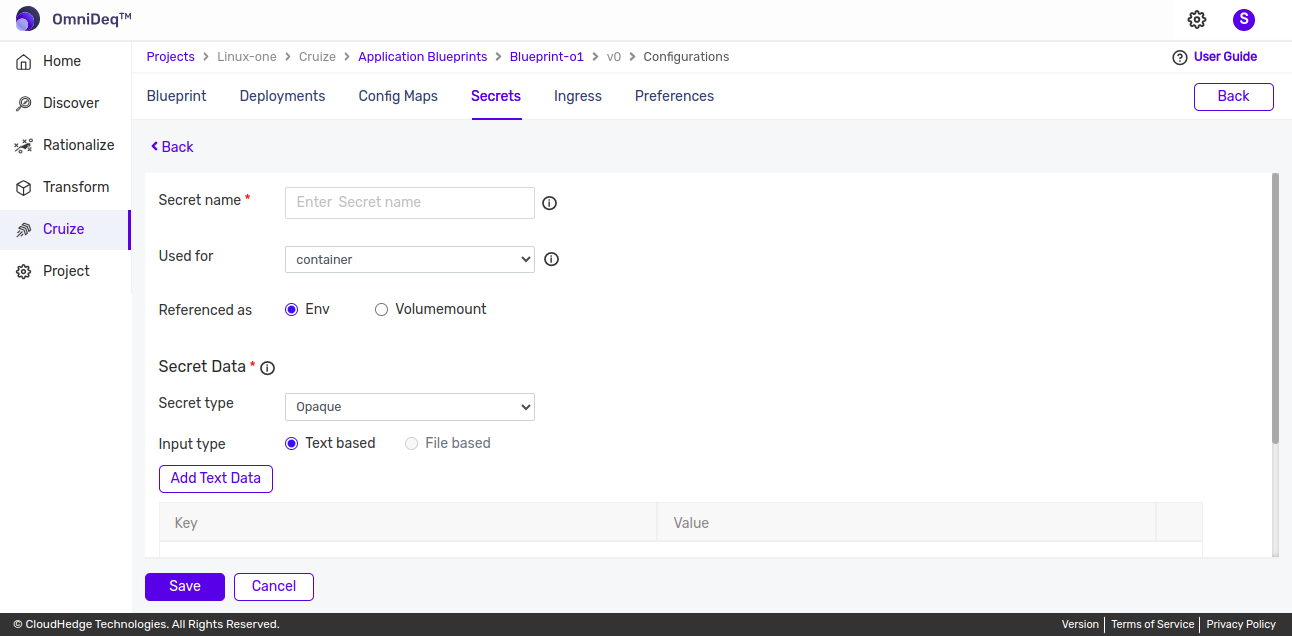
Note: If the blueprint is created from a transform profile, the secrets from the transform profile will be populated here.
-
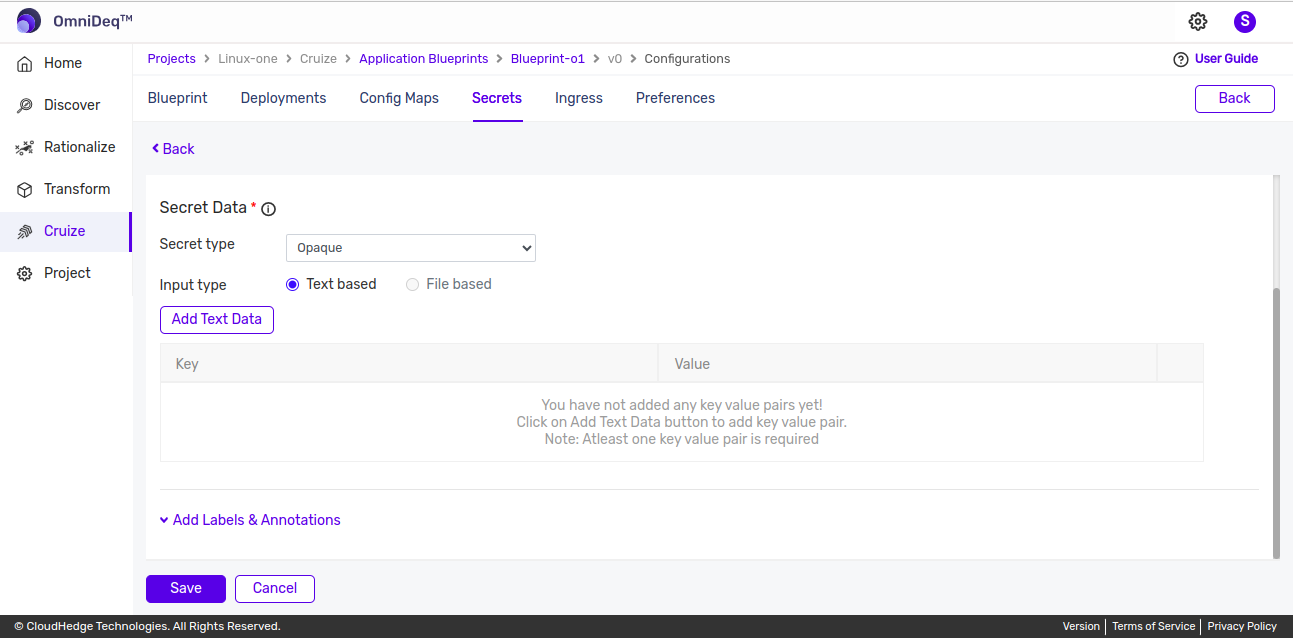
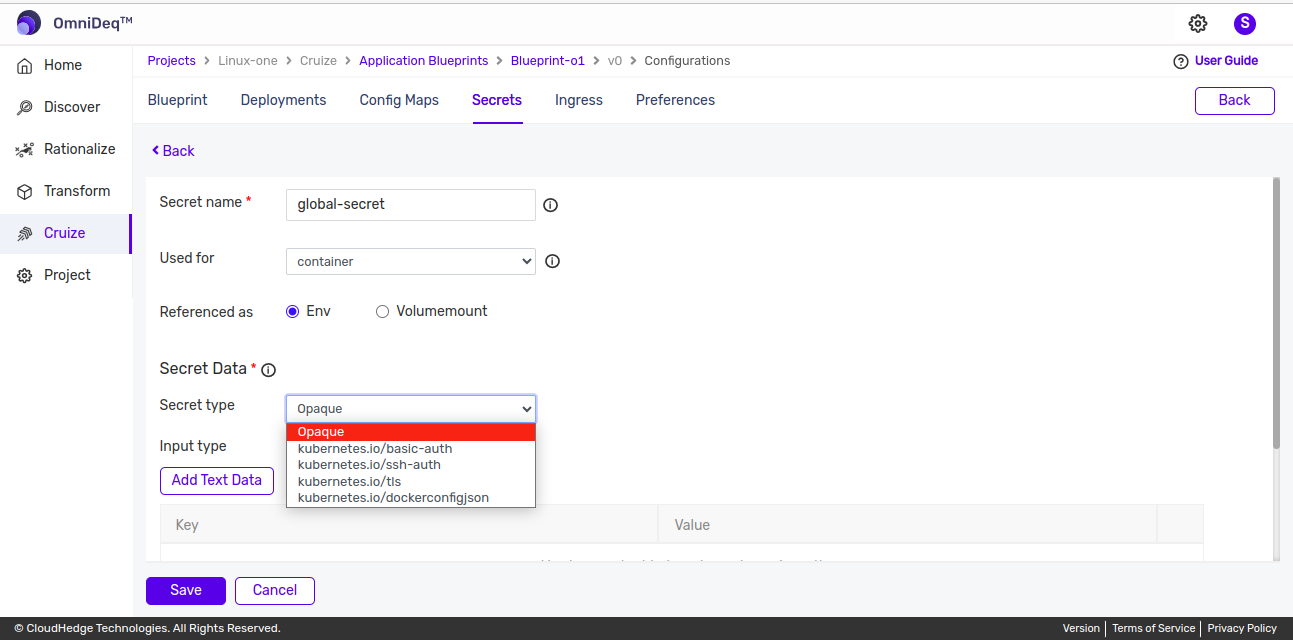
Add a secret by providing the following details:
Field Description Secret name Enter the secret name Used for Default selected is "Container", change as applicable Referenced as Default selected is "Env", change as applicable Input type Select applicable input type (Text-based/File-based) Add Text/File Data Based on input type, provide key values using text data or by uploading a file for the value Labels and Annotations Optional - Add labels and annotations here Secret Type There are 5 different secret types. Default selected is "Opaque". Enter secrets data based on the selected secret type.
1. Secret Name¶
Naming requirements: - Only lowercase alphanumeric characters, hyphens (-), or periods (.) are allowed - Must start and end with an alphanumeric character - Maximum 253 characters allowed - Name must be unique
2. Used For¶
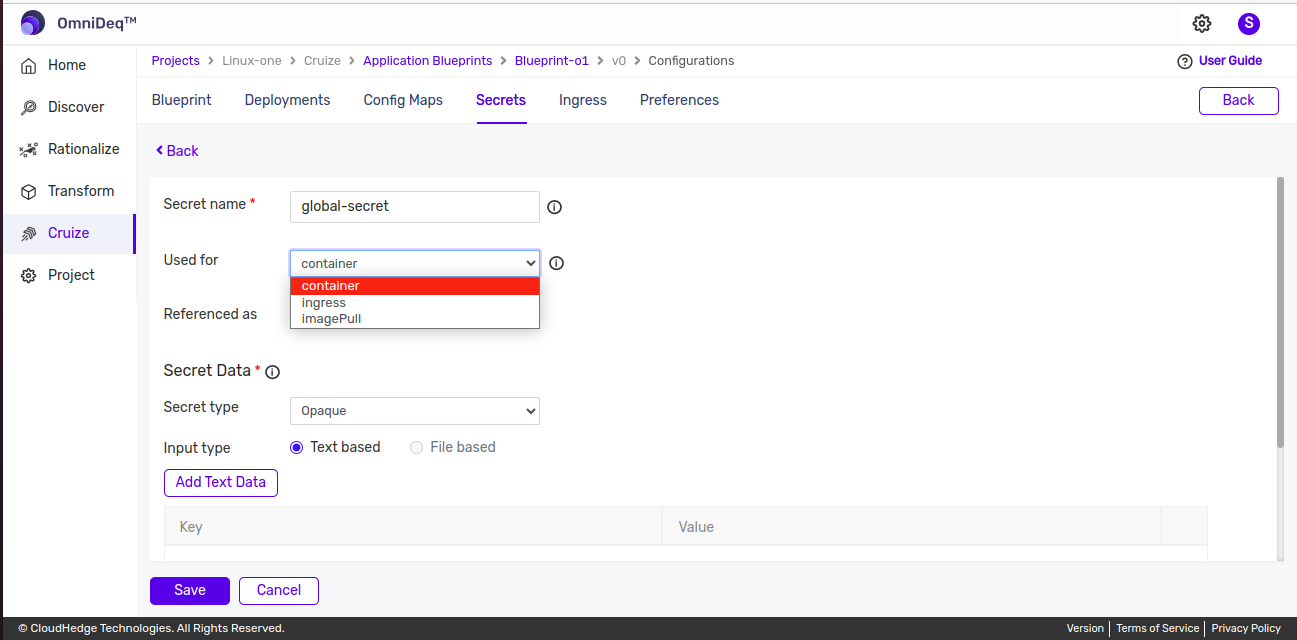
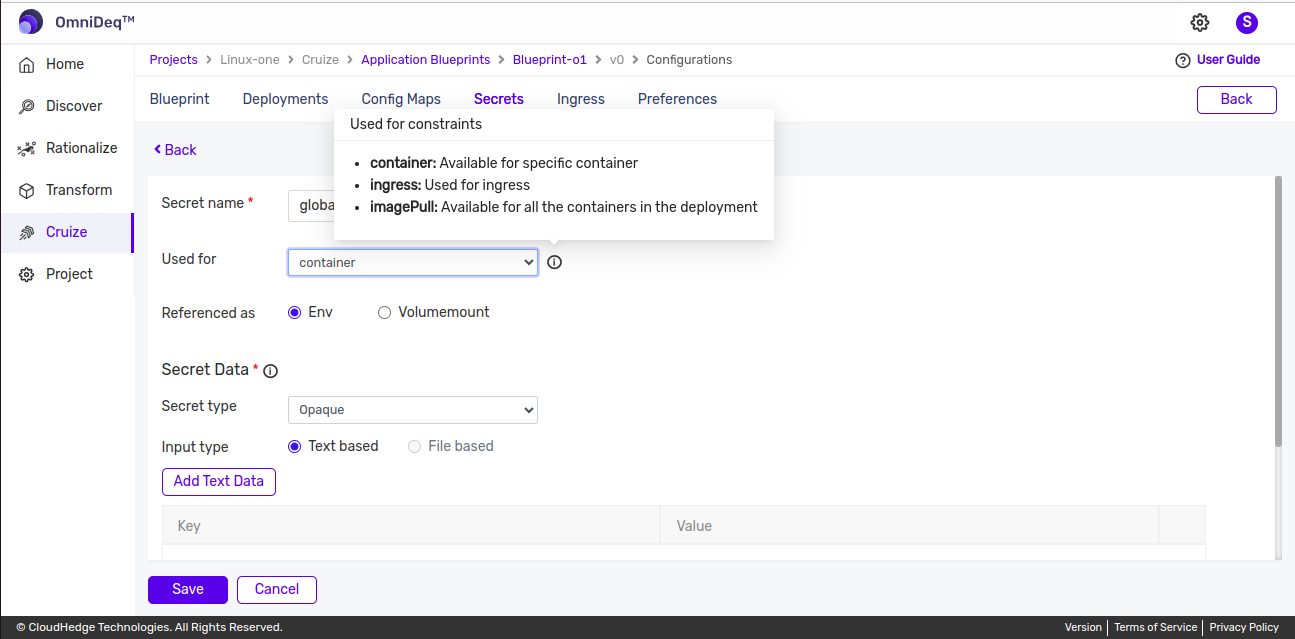
There are three options available in "Used for":
Container¶
For container secrets, any type of secret can be created, for example: opaque, basic-auth, or ssh-auth.
Ingress¶
For ingress secrets:
- Type will be kubernetes.io/tls
- Provide TLS certificate and TLS key
- Ingress secrets will be used to add ingress
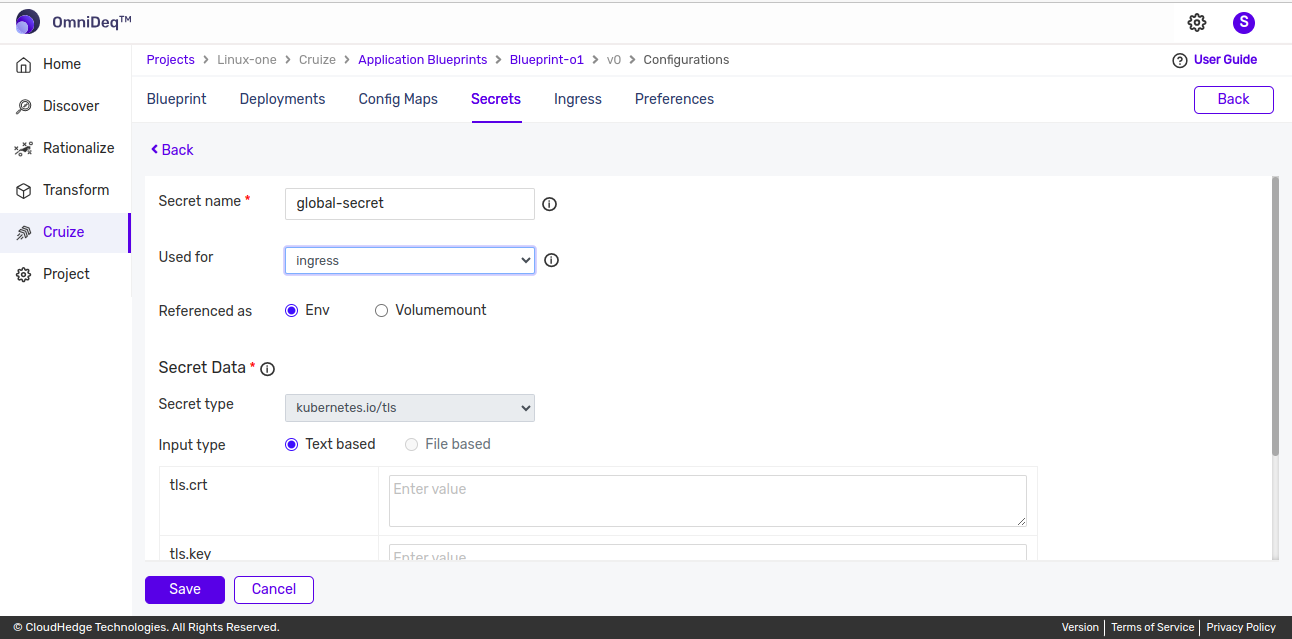
Image Pull¶
For image pull secrets:
- Type will be kubernetes.io/dockerconfigjson
- Provide Docker config JSON
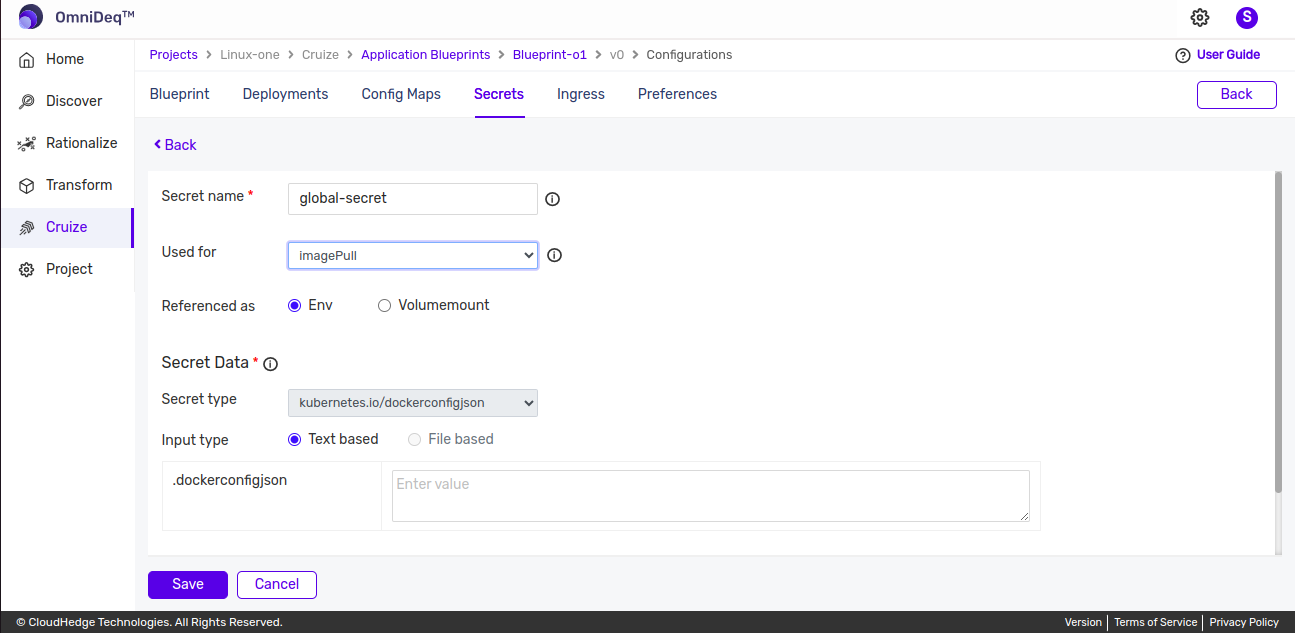
Image pull secrets can be added and used in deployments.
For more details on Adding Image Pull Secret in deployment, please refer to this section.
3. Referenced As¶
There are two options for "Referenced as":
Env¶
- For Env, you can only provide text-based config map data
Volume Mount¶
- For Volume Mount, secret data can be provided using text-based or file-based input
- Provide data based on the selected secret type
- For Volume Mount, provide the following details:
- Mount path: Enter the mount path, which should start with '/'
- Sub path: Optional
- Subpath key: Also optional, but if subpath is entered, you must provide a subpath key
4. Secret Type¶
There are five secret types available:
1. Opaque¶
For opaque type secrets, provide key-value pair data.
2. kubernetes.io/basic-auth¶
For kubernetes.io/basic-auth, provide username and password.
3. kubernetes.io/ssh-auth¶
For kubernetes.io/ssh-auth, provide ssh-privatekey.
4. kubernetes.io/tls¶
For kubernetes.io/tls, provide TLS certificate and key.
5. kubernetes.io/dockerconfigjson¶
For kubernetes.io/dockerconfigjson, provide Docker config JSON.
5. Labels & Annotations¶
Click here to learn more about labels and annotations.
Important Note:
Secret data can be provided either using text-based input or file-based input (file-based is only available for "Referenced as" Volume Mount).
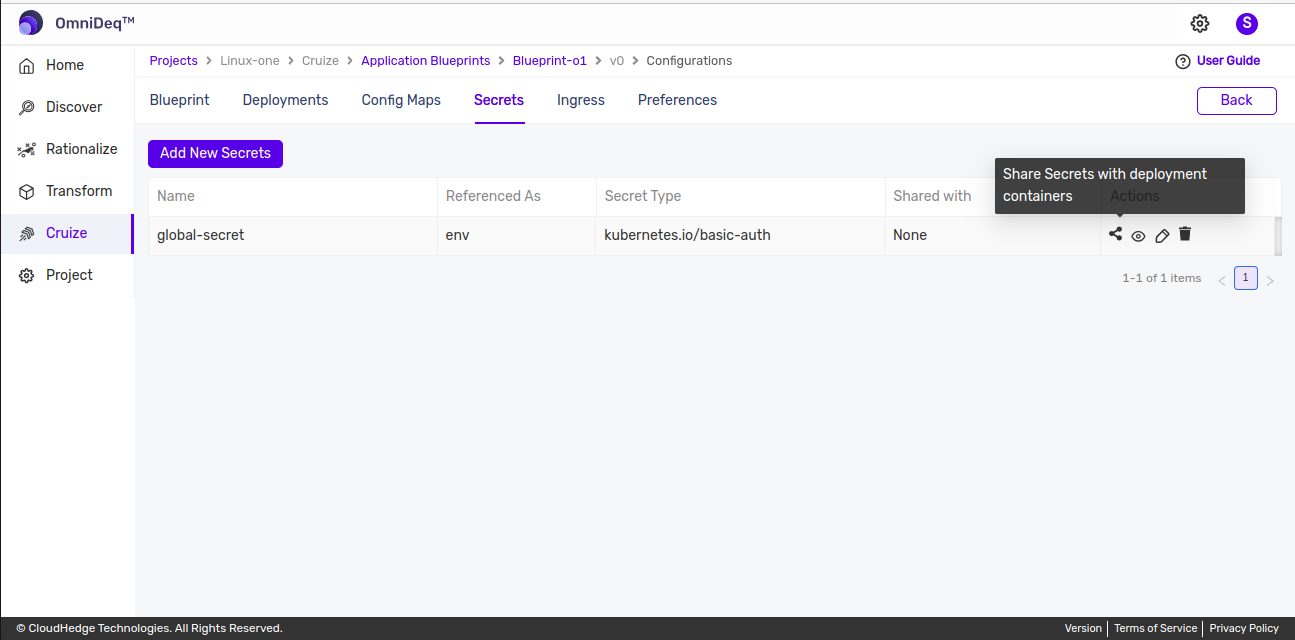
Share Secrets with Containers¶
Shared secrets can be shared with containers.
Steps to Share a Secret¶
-
Click the shareable icon from the actions column of the secret you want to share.
-
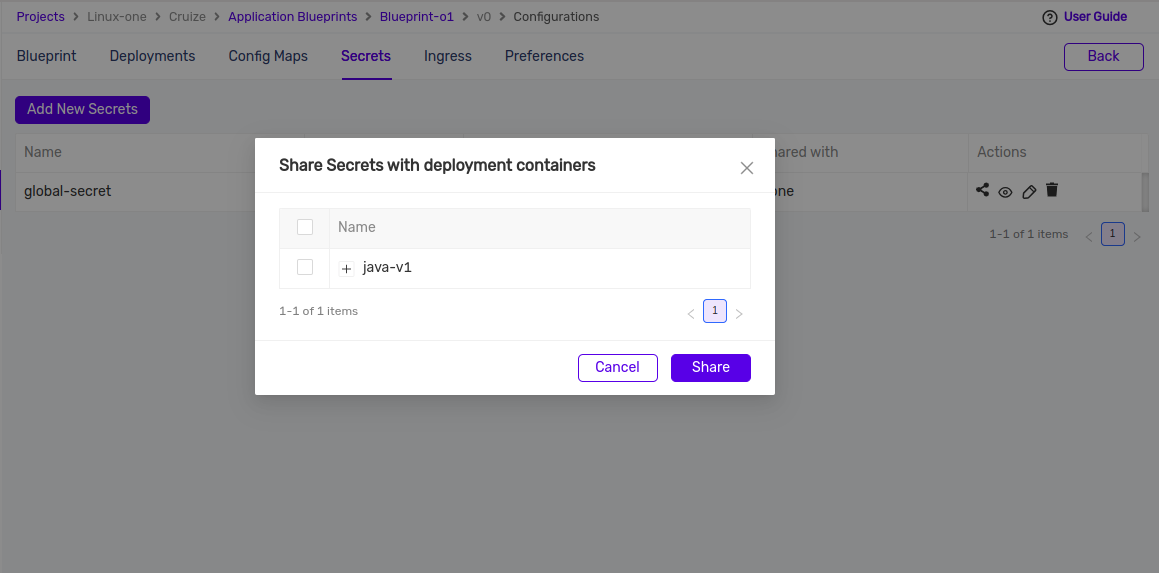
This will open a popup with a list of all containers from deployments added under the same blueprint, as shown in the image below.
-
A hierarchical list of deployments with containers will be shown in the popup. Select containers to share the secret with them, or to share with all containers under a deployment, select the deployment and all containers under that deployment will be selected.
-
After selecting containers, click the Share button. This will share the secret with the selected containers.
These shared secrets can be added to container secrets from containers.
For more details on Add Shared Secrets, please refer to this section.
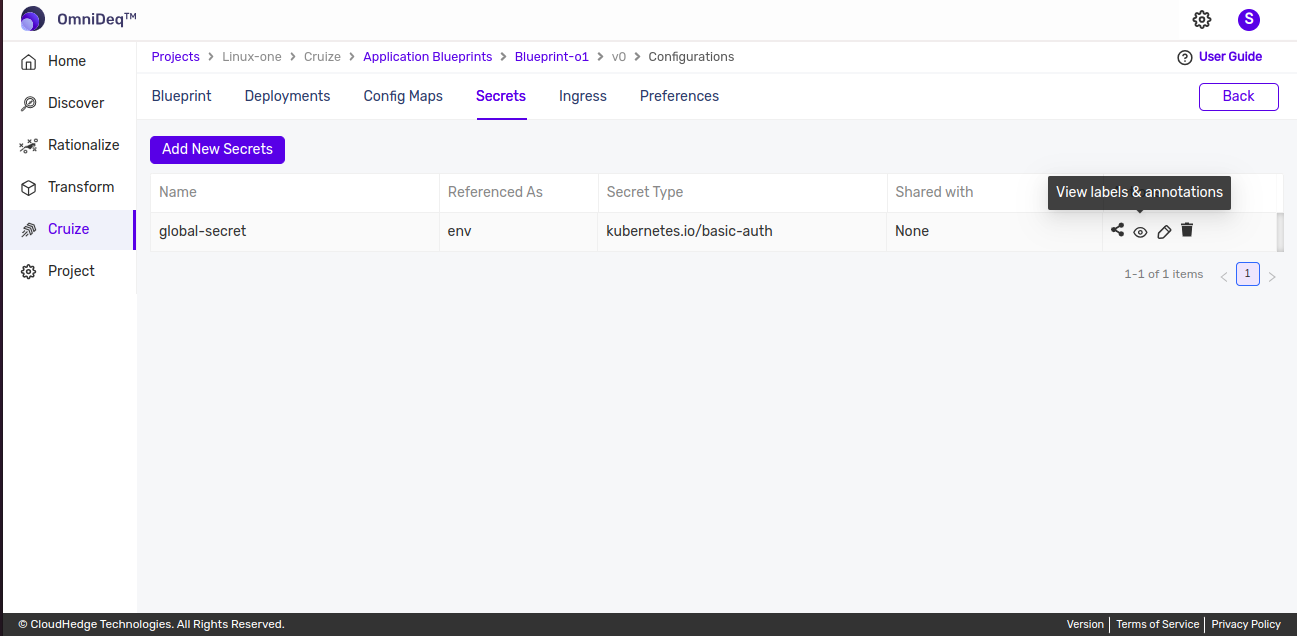
View Secret Labels & Annotations¶
To view labels & annotations:
-
Click the View (Eye) icon from the actions column in the secrets table as shown in the image below.
Edit Secrets¶
-
Click the Edit icon from the actions column in the secrets table to edit secret data as shown in the image below.
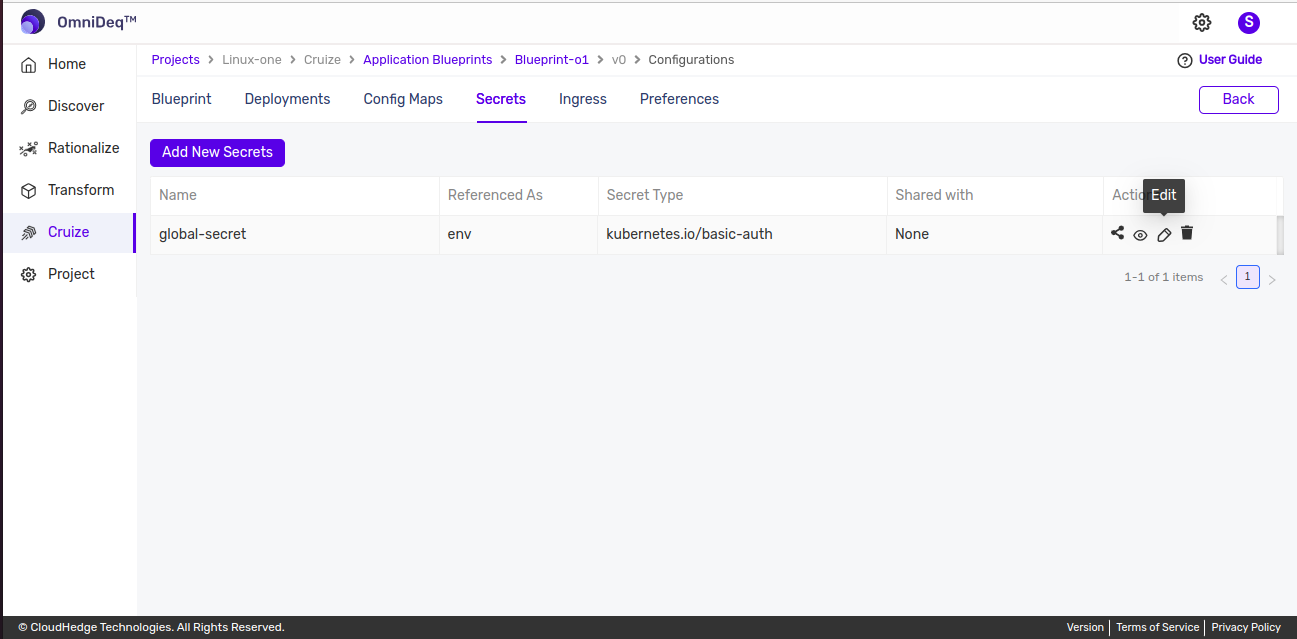
-
This will open a form with data to edit. After editing, click the Update button to save the changes.
Delete Secret¶
To delete a secret:
-
Click the Delete icon from the actions column of the secret as shown in the image below.
-
This will remove the deleted secret.